All of SSL.com’s email, client, and document signing certificates and NAESB client certificates can be used for client authentication in web applications. Certificate-based client authentication is a great way for businesses to add an additional authentication factor for employees who are working from home. With so many phishing scams out there, passwords alone are not enough to ensure good security!
This howto will show you how to use client certificates with the most popular desktop browsers. These instructions assume you have already downloaded and installed a PFX/PKCS12 file with your certificate and private key, or you have a hardware token with the certificate and private key inserted in the computer.
SSL.com certificates offering client authentication are available for as little as $20.00 per year for basic S/MIME email protection and ClientAuth. Our full-featured Business Identity certificates offer Organization Validation (OV) and trusted signatures for Adobe PDF, starting at $249.66 per year.
Google Chrome, Microsoft Edge, Internet Explorer, Apple Safari
Chrome, Edge, IE, and Safari are all configured to use client certificates and private keys provided by the OS. This includes PFX files imported into the OS certificate store, and certificates and private keys stored on smart cards (including SSL.com’s Business Identity certificates). So, if you’ve installed your PFX file or have your USB token inserted into the computer, you should already be good to go for client authentication with these popular desktop browsers.
Confirm Installation
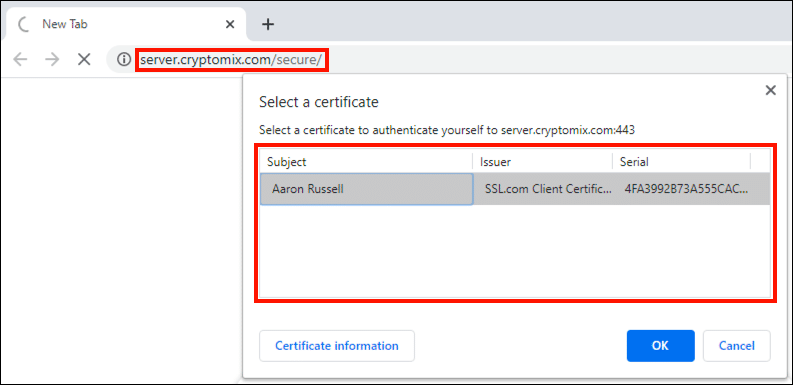
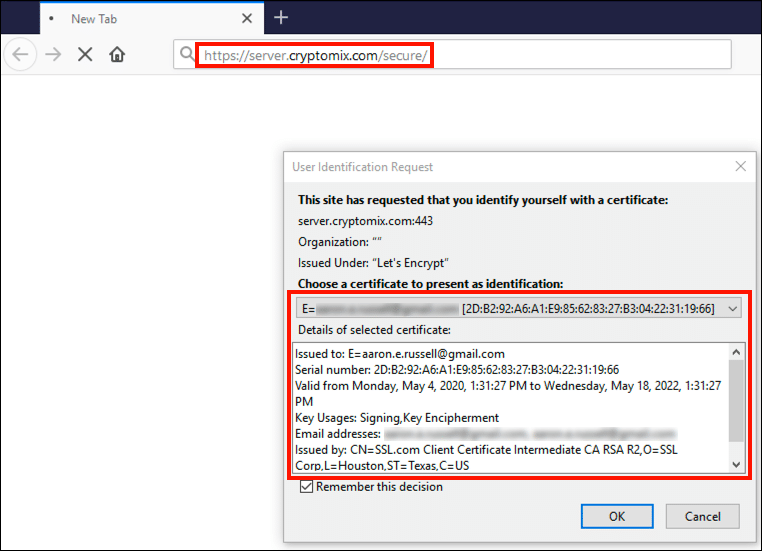
You can verify that installed client authentication certificates are available to your browser by navigating to https://server.cryptomix.com/secure/. If certificates are present, a dialog box will appear, listing them.
Mozilla Firefox
Use OS Certificate Store (Firefox 75 and Later)
Beginning with version 75, Firefox can be configured to use client certificates and private keys provided by the OS on Windows and macOS. This method supports both PFX files imported into the OS certificate store, and certificates and private keys stored on smart cards (including SSL.com’s Business Identity certificates). In general, this is now the preferred and simplest method to use client certificates in Firefox.
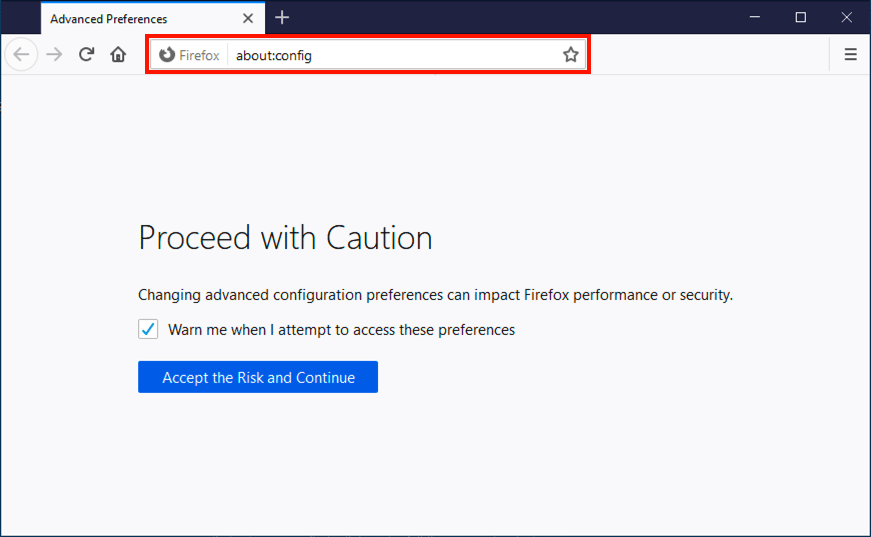
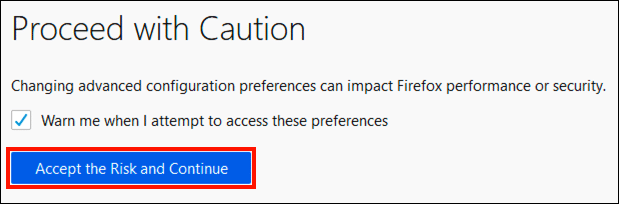
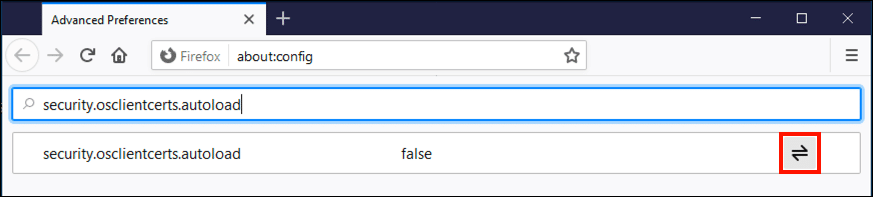
- Open Firefox and navigate to
about:configin the address bar. - If prompted, click Accept the Risk and Continue.
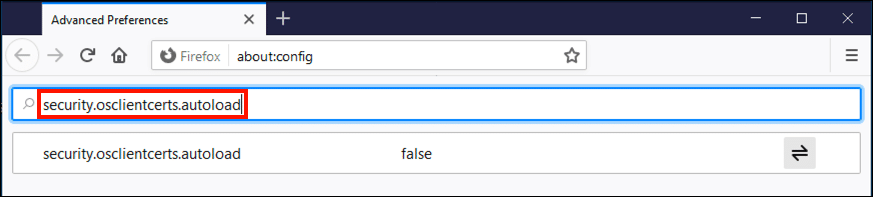
- Type
security.osclientcerts.autoloadinto the search field. - Click the Toggle button on the right side of the screen.
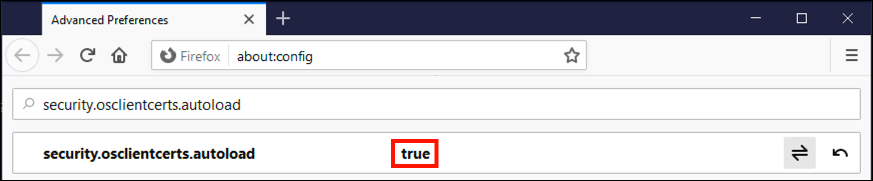
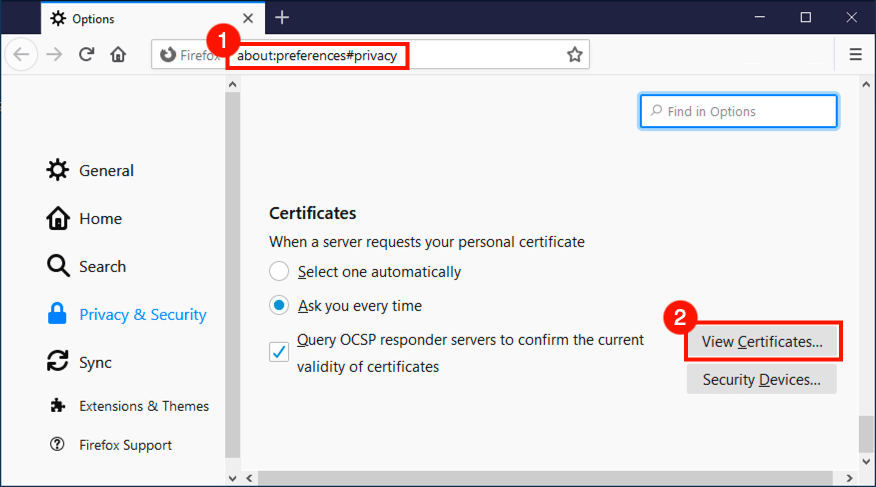
security.osclientcerts.autoloadis now set totrue, allowing the use of certificates provided by the operating system on Windows and macOS.- You can verify that Firefox can view certificates provided by the OS by navigating to
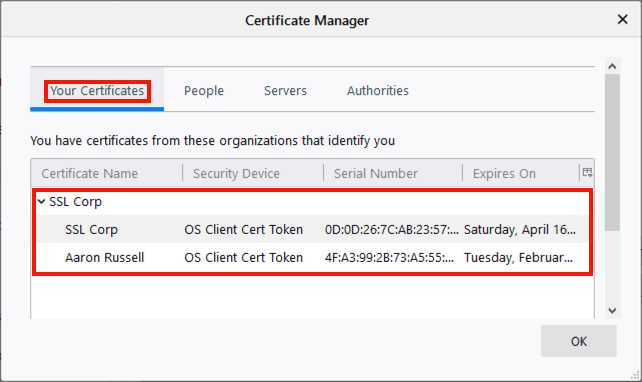
about:preferences#privacy, then scrolling down and clicking the View Certificates button. - Select the Your Certificates tab to display a list of personal certificates provided by the OS.
Install Client Certificates in Firefox
You can also install a certificate and private key directly into Firefox’s own certificate store by importing a PFX/PKCS12 file as described below. This method is not appropriate for certificates with non-exportable private keys stored on smart cards, including SSL.com’s Business Identity Email, ClientAuth, and Document Signing certificates.
- Open Firefox and navigate to
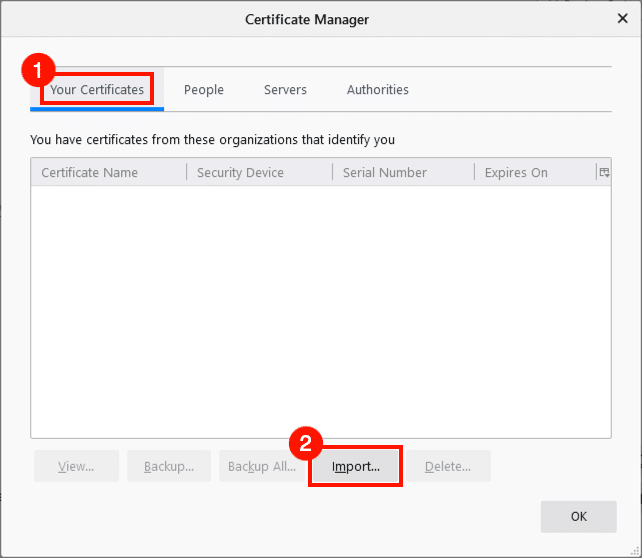
about:preferences#privacy, then scroll down and click the View Certificates button. - Select the Your Certificates tab, then click the Import button.
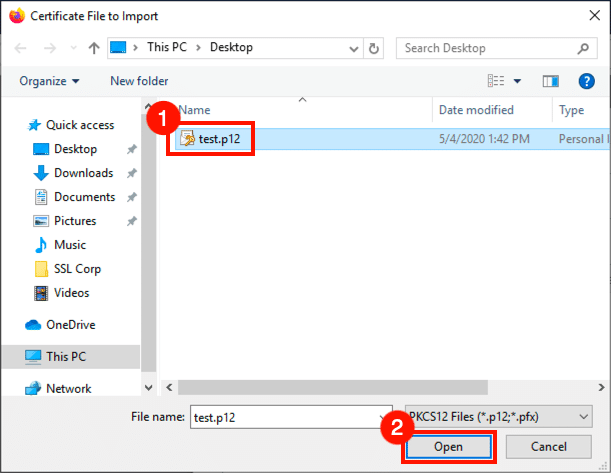
- Navigate to your PFX file, then click the Open button.
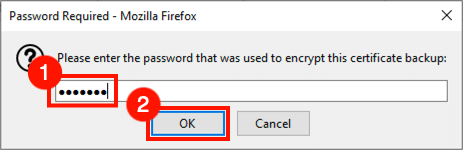
- Enter the password you created when downloading the PFX file from SSL.com, then click the OK button.
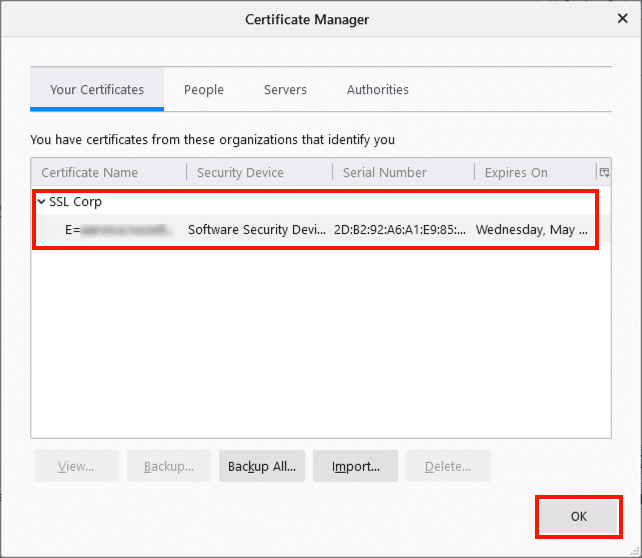
- The certificate is now installed in Firefox. Dismiss the dialog box by clicking the OK button.
Confirm Installation
You can verify that installed client authentication certificates are available to Firefox by navigating to https://server.cryptomix.com/secure/. If certificates are present, a dialog box will appear, listing them.