Certificate Authorities (CAs) have been a foundation of security online for the past two decades, and digital certificates continue to be a trusted method to ensure that transactions and identities are secure. On a fundamental level, CA-signed certificates are valuable tools that authenticate identities online; allow secure, encrypted communication over otherwise insecure networks; and confirm the integrity of signed documents by verifying they have not been altered by a third party.
But the value of CAs extends past their immediate practical usefulness. What is a very simple verification process for the user is underpinned with a lattice of work and chain of trust that goes beyond a simple fact check.
What do CAs do?
Browser and operating system vendors trust public CAs (such as SSL.com) to verify:
- Control of domain names
- The legitimacy of organizations and their agents
- Contact information such as email addresses
CAs issue many types of certificates, all based on the X.509 standard. CA-issued certificates ensure that website transactions are secure, protect against malware, and authenticate documents and email exchanges.Establishing identities on the internet is done through a variety of processes, procedures, and protocols, all assured by CAs. For example:
- SSL/TLS provides a trusted and encrypted means to access the World Wide Web through browsers – which protects personal information and transactions.
- Digital Signatures provide authenticated digital documents.
- Code Signing allows for safe distribution of software on the Internet.
- S/MIME enables authenticated and encrypted email.
- Client Authentication certificates protect access to computers and applications.
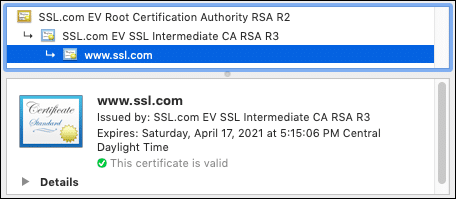
All of this is done through certificates that are anchored to a public CA’s root certificate, and linked together via a “chain of trust”:
Why is it so hard to be a publicly trusted CA?
As outlined above, CAs are trusted by operating systems and other software to verify the identities of websites, companies, and individuals. Once a public CA is established and earns the trust of software vendors and other players, its digital certificates are an instant, secure and reliable way to make sure that information isn’t fraudulent. The process for making a self-signed root CA is relatively simple – they honestly could be created by anyone with widely-available, low- or no-cost software. However, there really aren’t very many public certificate authorities. In fact, there are currently only 52 CA members of the CA/Browser Forum, and the vast majority of SSL/TLS certificates come from a smaller number than that. So why isn’t everyone making them?
The reason that public certificate authorities are such an exclusive club is that becoming a public CA and earning and maintaining the universal trust to keep it functional is a lot of work. Inclusion in all of the browsers and operating systems is seamless on the user’s end of things, but it requires years of legwork behind the scenes. When you buy a new computer or install software such as a web browser or email client, a list of trusted root CA certificates is already included. But getting added to that list not something that just happens overnight, and staying there is a challenge too.
To stay in business selling certificates, a CA must satisfy the requirements of software vendors, who are all trying to ensure a secure and reliable experience for their users. Each major browser and operating system vendor has its own set of criteria that CAs must meet and keep pace with when changes are made. The cost of not doing so is high: if a CA isn’t included in any one of the root programs, whether it’s due to a breach of trust or because of a failure to stay current with policy changes, it would spell disaster for the entire business. No company is looking for a website SSL certificate that works with Safari but not Chrome. Few software producers would want a code signing certificate that Windows doesn’t trust.
In addition to maintaining this delicate balance with browsers, operating systems and other software providers, Certificate Authorities are subject to rigorous outside audits. See those badges at the bottom of this very site? Each of those seals represents an audit, and each of those audits are done annually. Should any CA fail an audit (or fail to meet root program requirements) that CA’s certificates could be excluded from crucial root stores, which would render them useless.
The CA members of the CA/Browser Forum (a consortium of CAs and vendors of PKI-enabled software such as browsers and operating systems) are active in developing and enforcing dozens of industry standards and setting the CA/B Forum Baseline Requirements. Members participate in educational and research organizations, and collaborate with stakeholders to strengthen internet security, often taking the lead on proposing and adopting new standards. CAs have the most interest in making sure the SSL/TLS system is working and its reputation is sound, which necessarily means that they take a proactive and aggressive tack towards the security of their systems and of the systems they work with.
In addition to adhering to these standards, certificate authorities are required to maintain and make available certificate transparency lists (public records of all issued certificates), as well as certificate revocation lists (CRLs) and OCSP responders, which keep track of revoked certificates. It is of paramount importance to make sure that all certificates are accounted for, and that the trust that underpins certificates is never broken.
How to choose a CA
So, knowing all of the work that goes into maintaining and running a public certificate authority, how does one determine which CA is best for their needs?
Though there are now low-cost (or even free) CA options, it’s important to know what is being traded for that reduced cost. In general, free CAs don’t offer the same validation levels as commercial CAs, and do not offer anything other than website SSL/TLS certificates. For example, they can show that an applicant for a website SSL/TLS certificate controls that domain (Domain Validation) but they don’t take the extra step of affirming who that owner is. Depending on your intended use case, DV may be fine (all commercial CAs, including SSL.com, offer it too), but if you need a code signing certificate, digital signatures for Adobe PDFs, or validated information about your business included in your website certificate, you need to go to a commercial CA.
For more information on choosing a reliable CA, please check out our Best Practices Guide.



