LDAP (Lightweight Directory Access Protocol) is an industry-standard protocol for accessing and managing directory information services. It is commonly used for storing and retrieving information about users, groups, organizational structures, and other resources in a network environment.
Integrating LDAP with S/MIME certificates and client authentication certificates involves utilizing LDAP as a directory service to store and manage user certificates.
By integrating LDAP with S/MIME certificates and client authentication certificates, organizations can centralize certificate management, enhance security, and streamline the process of certificate retrieval and authentication in various applications and services that leverage LDAP as a directory service.
Requirements
- An Enterprise PKI (EPKI) Agreement. The article Enterprise PKI (EPKI) Agreement Setup provides instructions for this.
- An approved request to be an EPKI Administrator. The steps below illustrate how to do this using your SSL.com account.
- Login to your SSL.com account.
- Click the Dashboard tab on the top menu.
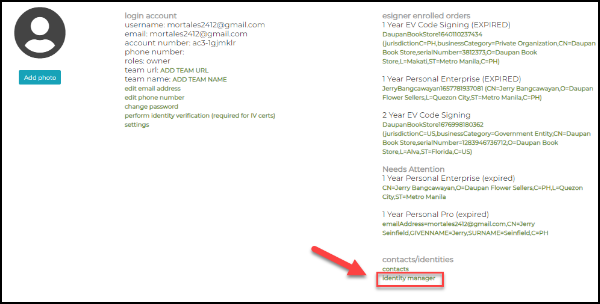
- Scroll down to contacts/identities section and click the link to identity manager.
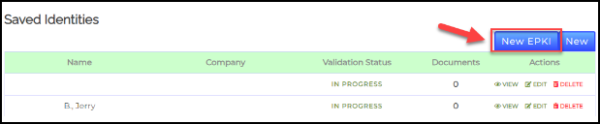
- Click the New EPKI button.
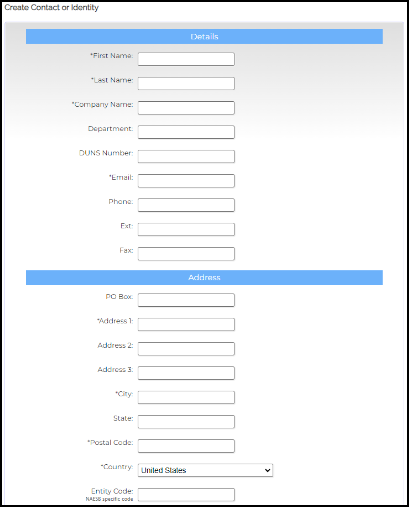
- Fill out the required fields for contact information. These include First Name, Last Name, Company Name, Email, Address 1, City, Postal Code, & Country.
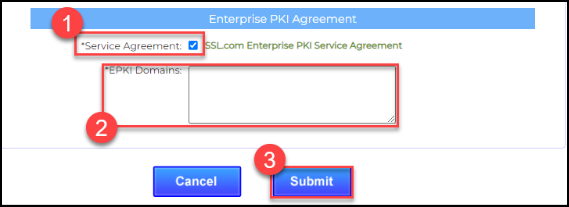
- Tick the check box for Service Agreement and then place the domain address that you will be using. Once everything is finalized, click the Submit button.
- After submitting your request to be an EPKI Administrator, contact support@ssl.com for its approval.
Create LDAP Setting
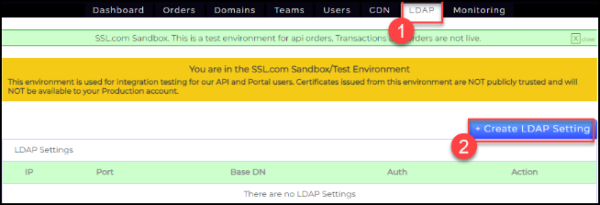
- Login to your SSL.com account and click the LDAP tab on the top menu, followed by the + Create LDAP Setting button.
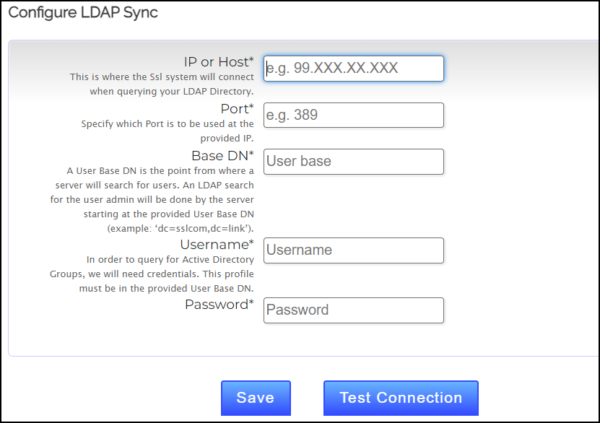
- Configure LDAP Sync. Fill out the required fields to implement the LDAP integration. Afterwards, click the Save button followed by the Test Connection button.
- IP or Host – This is where the Ssl system will connect when querying your LDAP Directory.
- Port – Specify which Port is to be used at the provided IP.
- Base DN – A User Base DN is the point from where a server will search for users. An LDAP search for the user admin will be done by the server starting at the provided User Base DN (example: ‘dc=sslcom,dc=link’).
- Username – In order to query for Active Directory Groups, we will need credentials. This profile must be in the provided User Base DN.
- Password
Use LDAP for Issuance of S/MIME Certificates
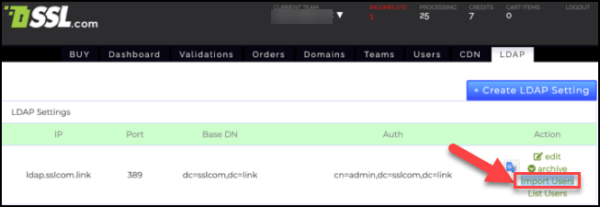
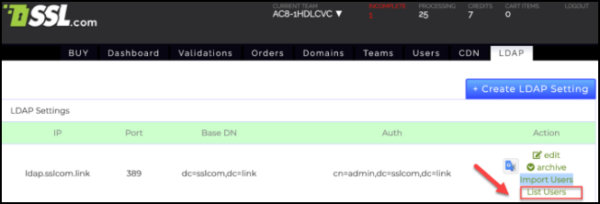
- Once the settings are created, it will look like the following. Click import users so that the users from LDAP connection will be imported to SSL.com’s system.
- Click List Users so that the imported users can load.
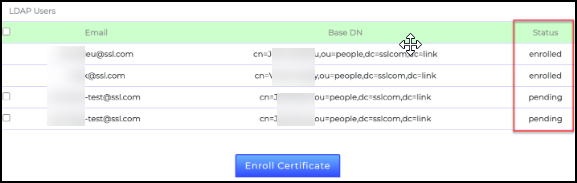
- Under the Status column, you will see enrolled, processing, or pending.
- enrolled – This means the certificate has been created in ssl.com and added to LDAP
- processing – This means the certificate order has been created but not validated and the certificate has not been generated.
- pending – this means the user has not yet requested for any certificate enrollment.
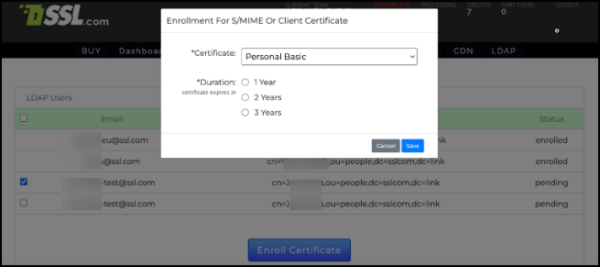
- For users assigned to pending status, there is a checkbox to select the user and enroll an S/MIME certificate order.
- Each user will be assigned a new certificate order from here. The process will then proceed to order validation and certificate issuance.
- After successful issuance of the certificate, it can be added or replaced to LDAP users