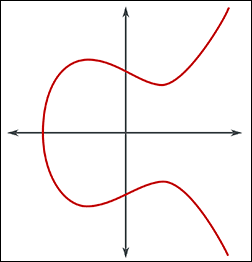
Elliptic curve cryptography (ECC) uses the mathematical properties of elliptic curves to produce public key cryptographic systems. Like all public-key cryptography, ECC is based on mathematical functions that are simple to compute in one direction, but very difficult to reverse. In the case of ECC, this difficulty resides in the infeasibility of computing the discrete logarithm of a random elliptic curve element with respect to a publicly known base point, or the “elliptic curve discrete logarithm problem” (ECDLP)1. The Elliptic Curve Digital Signature Algorithm (ECDSA) is a widely-used signing algorithm for public key cryptography that uses ECC.
Performance
For most users, the important point to remember is that, compared to the more mature and widely-used RSA algorithm, ECDSA offers equivalent cryptographic strength with much lower key sizes. Although symmetric encryption is the most performant scheme used today, some form of asymmetric encryption is necessary for a secure SSL/TLS handshake. ECC algorithms offer the closest asymmetric equivalent to symmetric encryption in terms of performance. As shown in the table below, ECDSA key sizes increase linearly with symmetric encryption keys of equivalent strength (as 2× the symmetric key size), while RSA keys rapidly become much larger:
| Equivalent Key Size (bits) | ||
|---|---|---|
| Symmetric | ECDSA | RSA |
| 80 | 160 | 1024 |
| 112 | 224 | 2048 |
| 128 | 256 | 3072 |
| 192 | 384 | 7680 |
| 256 | 512 | 15360 |
ECDSA’s smaller key sizes mean that stronger encryption can be achieved with less computing power and network bandwidth than RSA; this is especially advantageous for low-powered mobile and Internet of Things (IoT) devices, which are becoming increasingly ubiquitous.
ECDSA has been endorsed by the US National Institute of Standards and Technology (NIST), and is currently approved by the US National Security Agency (NSA) for protection of top-secret information with a key size of 384 bits (equivalent to a 7680-bit RSA key).
1. Source: Wikipedia (Elliptic-curve cryptography)