Introduction
Ranging from home security cameras and door locks to set-top boxes, thermostats, kitchen appliances, medical devices, and traffic lights, the number of Internet-connected devices has been growing at a staggering rate since the early 2000’s. Estimates vary, but according to an infographic published by Intel, the IoT, which included 2 billion “smart” objects in 2006, is projected to increase a hundredfold to 200 billion devices by 2020. For perspective, that’s 26 IoT devices for every human on the planet.
Need a Certificate? SSL.com provides a wide variety of digital certificates, including:
The IoT’s explosive growth has been accompanied by serious security flaws and growing pains. A 2017 survey of approximately 400 IT executives by Altman Vilandrie & Company indicates that almost half of the firms surveyed had experienced at least one IoT-related security breach, and that the cost of the breaches represented “13.4% of the total revenues for smaller companies and hundreds of millions of dollars for the biggest firms.”
Closer to home for most consumers, frightening news stories about vulnerable security cameras and smart locks are increasingly common. At DEF CON 2016, researchers from Merculite Security highlighted multiple security vulnerabilities in commonly available smart locks, including four manufacturers shipping locks that used plain-text passwords. Anyone monitoring network communication with such a lock could easily retrieve the password, not acceptable for a device intended to keep families, homes, and property secure.
SSL/TLS for the IoT
Manufacturers and vendors of Internet-connected smart devices can no longer afford to be complacent about security as society becomes both increasingly dependent on their products and aware of vulnerabilities. One important step that IoT businesses can take is to install publicly trusted SSL/TLS certificates for authentication and encryption on their devices.
The SSL/TLS protocol uses asymmetric encryption to secure data shared between two computers on the Internet. In addition, SSL/TLS ensures that the identities of the server and/or client are validated. In the most common scenario, an HTTPS server provides visitor’s browser with a certificate which has been digitally signed by a publicly trusted Certificate Authority (CA) like SSL.com. The mathematics behind SSL/TLS ensure that a CA’s digitally signed certificates are practically impossible to falsify given a large enough key size. Public CAs verify the identity of applicants before issuing certificates. They are also subject to rigorous audits by operating system and web browser providers to be accepted and maintained in trust stores (lists of trusted root certificates installed with browser and OS software).
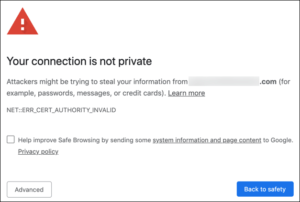
Put simply, if a website has a certificate signed by a publicly trusted CA, web browsers and operating systems can trust that the owner of the site is, in fact, who they claim to be. Users attempting to access websites that present a certificate that is not publicly trusted will be met by stern security warnings and roadblocks that must be clicked through. This same basic principle of authentication through x.509 certificates can be applied to email communication, computer code, and IoT devices.
SSL/TLS can also be used to authenticate clients. For example, a company may wish to allow only certain employees to access a web-based application, and, through issuing client certificates to those employees, can use the certificates as credentials for access.
Both SSL/TLS client and server authentication have important implications and uses for the IoT. Most of us have seen messages like this before when attempting to connect to a home wireless router with a self-signed certificate:
With publicly trusted SSL/TLS certificates, your customers will never encounter messages like that on your device’s admin interface. Returning to the example above, SSL/TLS certificates could be used to greatly strengthen security in that Internet-connected “smart” door lock, by:
- Installation of a publicly trusted server certificate in the lock, so that a user connecting to its web-based interface will not have to click through a security warning and/or add a security exception for a self-signed certificate;
- Requiring a client certificate on the user’s smartphone to access the lock’s interface; and/or
- Encrypting any communication between the client and the lock, or between the lock and its provider’s servers. No more plain-text passwords!
Manufacturers may also install publicly trusted client certificates in their devices to authenticate themselves with third-party providers. For example, a manufacturer of Internet-connected set-top boxes could use SSL/TLS certificates for mutual authentication when connecting to streaming audio and video providers.
Performance Concerns
One common concern about integrating Internet PKI with the IoT is the idea that SSL/TLS is too computationally expensive for small, low-powered devices to handle, and for some older legacy devices this may be true. However, the overhead of the SSL/TLS protocol is not necessarily all that significant when measured against the cost of transmitting the data in the first place, especially as the size of a transaction rises. A 2011 study of the energy consumed by mobile devices using TLS indicates that while SSL/TLS overhead is significant for very small transactions of less than 10KB, “with transactions larger than 500KB, the energy required to transmit the actual data clearly outranks the TLS energy overhead.”
Currently, there are multiple lightweight implementations of the TLS protocol available to meet the constraints of low-powered IoT devices. The open-source TLS Toolkit (formerly MatrixSSL) can be configured to a code footprint of only 66KB, and even smaller footprints are possible with manual optimization. wolfSSL, another open-source SSL/TLS library, advertises a minimum footprint size of 20-100KB, and runtime memory usage of 1-36KB. Clearly, these numbers are already achievable even for a device of very modest specifications, and we can expect to see further optimization of software combined with increased power at lower cost for embedded devices going forward.
How SSL.com Can Help IoT Manufacturers
SSL.com offers these world-class services and benefits to our business customers in the IoT space:
- Custom Solutions: As the experts in SSL/TLS, SSL.com collaborates with IoT manufacturers to optimize the generation, installation, and lifecycles of certificates for their devices.
- Subordinate CA: A hosted subordinate CA (also known as an issuing CA) from SSL.com offers manufacturers complete control over the issuance of publicly trusted end-entity certificates for their devices, at a small fraction of the cost of establishing their own root CA and private PKI infrastructure.
- Management Tools: SSL.com‘s online management tools allow device manufacturers to easily issue high volumes of certificates and manage their lifecycle.
- API: IoT manufacturers can automate certificate issuance and lifecycle with SSL.com‘s SSL Web Services (SWS) API.
- ACME: Manage certificate lifecycles on IoT devices with a custom ACME-enabled issuing CA. ACME is an established, standard protocol for certificate management with many open-source client implementations.
As the number of IoT devices increases exponentially, SSL.com has all the tools and expertise needed to help manufacturers and vendors manage the installation and lifecycle of publicly trusted security certificates on even the most performance-constrained hardware. If it’s connected to the Internet, we can help you secure it! Please contact us by email at Support@SSL.com or call 1-SSL-Certificate (1-775-237-8434) if you have any questions or would like more information on SSL.com‘s IoT solutions. And, as always, thank you for choosing SSL.com!