This article will show you how to disable SSL 3.0 and TLS 1.0 in your browser.
Introduction
After the recent POODLE unpleasantness, both Google and Chrome secured their latest browser versions (Firefox 35, Chrome 40) by barring the use of the SSL 3.0 encryption protocol entirely, since POODLE utilizes this protocol as an attack vector. (Microsoft has released various patches and quick-fixes for Internet Explorer 11 and states they’ll completely disable SSL 3.0 in April 2015.)
Disabling SSL 3.0 is definitely a Good Thing. However, the subsequent revelation that TLS 1.0 is also vulnerable seems to have caught them on the off foot – TLS 1.0 is still enabled by default in all three major browsers as of this writing. In this article, we will show you how to protect yourself by forcing your browser to use only the safer TLS 1.1 and TLS 1.2 protocols.
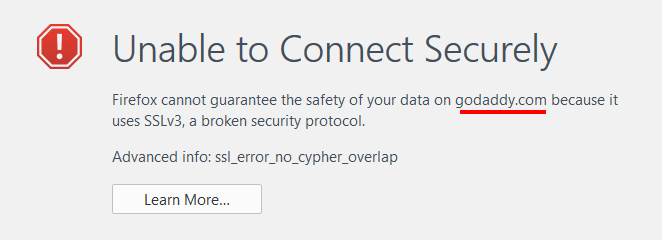
NOTE: POODLE and similar exploits work when both the server and browser ends of a supposedly safe connection can be tricked into using an obsolete protocol. If you have secured your browser to only use TLS 1.1/1.2 but the website’s server still relies on older, insecure protocols, be aware that you may have issues connecting to that site.
Internet Explorer
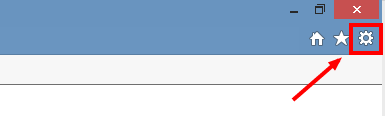
- Left-click the gear icon:
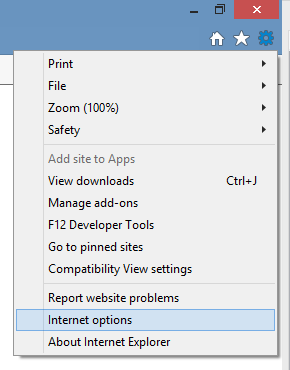
- Select “Internet options” from the dropdown menu:
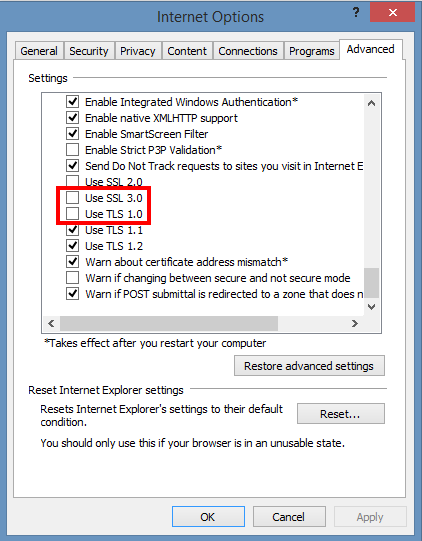
- Click the “Advanced” tab, scroll down and deselect “SSL 3.0” and “TLS 1.0”.
- Click “OK” to accept your changes, which should take effect immediately. (You may need to refresh your browser.)
Firefox
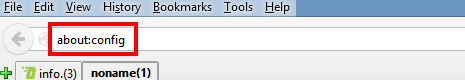
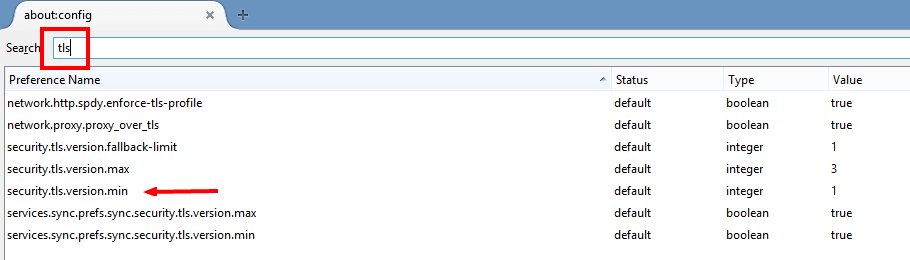
- In the address bar, type “about:config” and hit enter.
- In the “Search” field, enter “tls”. Find and double-click the entry for “security.tls.version.min”.
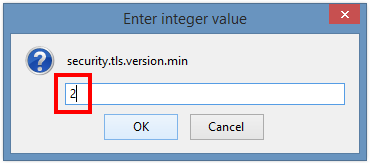
- Set the integer value to “2” to force a minimum protocol of TLS 1.1 (entering “3” would force TLS 1.2).
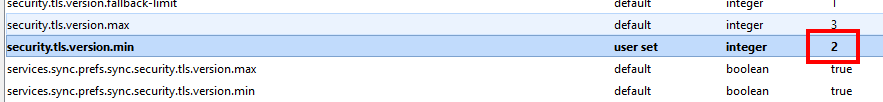
- This configuration will now show the new value and will take effect immediately (don’t forget to clear your cache).
Chrome
Science marches on! A massive tip of the hat (or tip of the massive hat) to commentator John Giles for pointing out that using chrome://flags/ is the latest and easiest way to set the minimum protocol version in Chrome. We must note that Google hangs a red warning over using flags – however, our testing has yielded positive results.John says:
For Chrome, how about this?:
chrome://flags
Under “Minimum SSL/TLS version supported.”, change from “Default” to “TLS 1.1?.
Then press the “Relaunch Now” button at the bottom of the page.
Thanks again, John!
Unlike IE and Firefox, Chrome can only be made to use TLS 1.1/1.2 by a command-line switch – an argument added to the string that fires up the browser. This can be implemented by setting up a shortcut as we will show you below, but note that ONLY starting Chrome from this shortcut will prevent use of insecure protocols.
To create a secure shortcut:
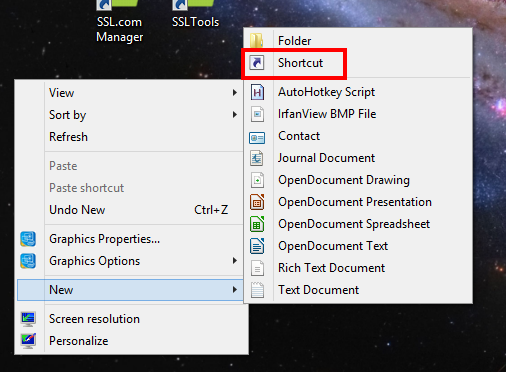
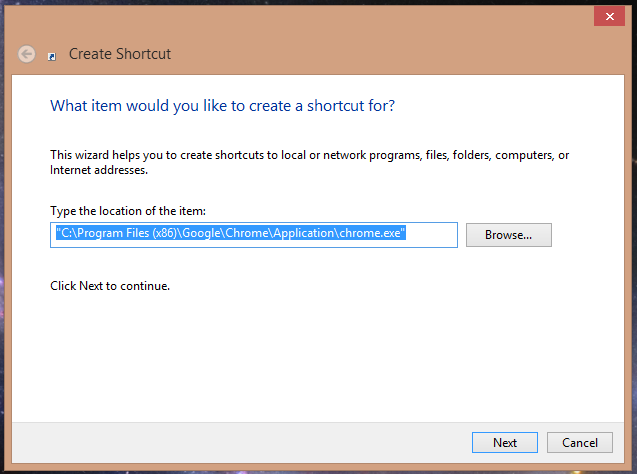
- Right-click on your desktop and select “New”, then “Shortcut”.
- In the “Create Shortcut” panel, browse to the location of your Chrome installation and select the Chrome icon – the default location is:
C:Program Files (x86)GoogleChromeApplicationchrome.exe
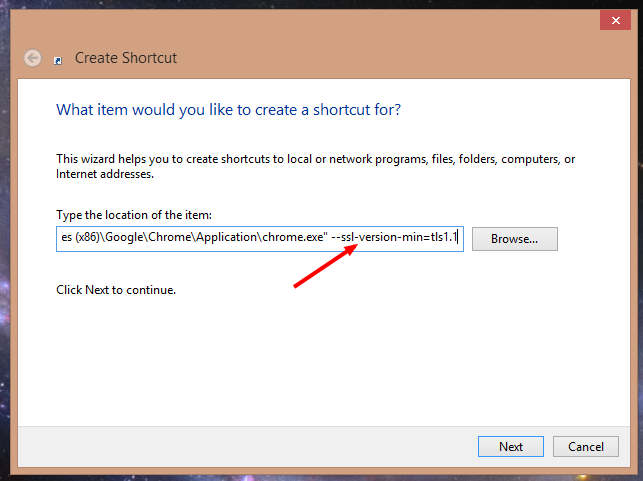
- Add the following command line switch
--ssl-version-min=tls1.1after the item location (i.e., after the ending quote) to appear thus:"C:Program Files (x86)GoogleChromeApplicationchrome.exe" --ssl-version-min=tls1.1
Make sure and separate the switch from the location with a space.
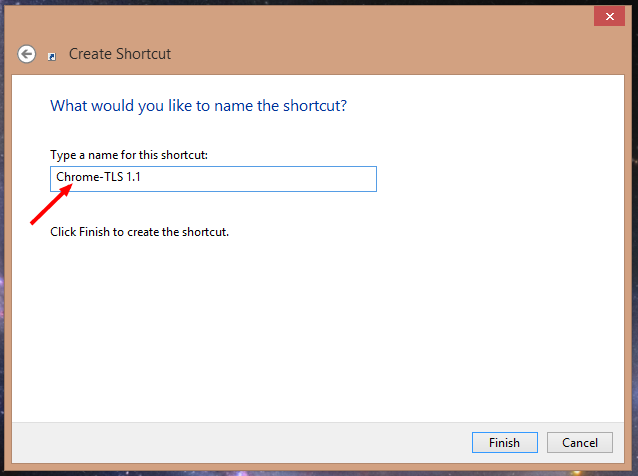
- Name the shortcut (SSL.com suggests giving it a unique name which will remind you that this shortcut is secure) and click “Finish.”
- Again, the only way to be certain that your Chrome session is secure will be using your new shortcut.